Privileged Access Management Software
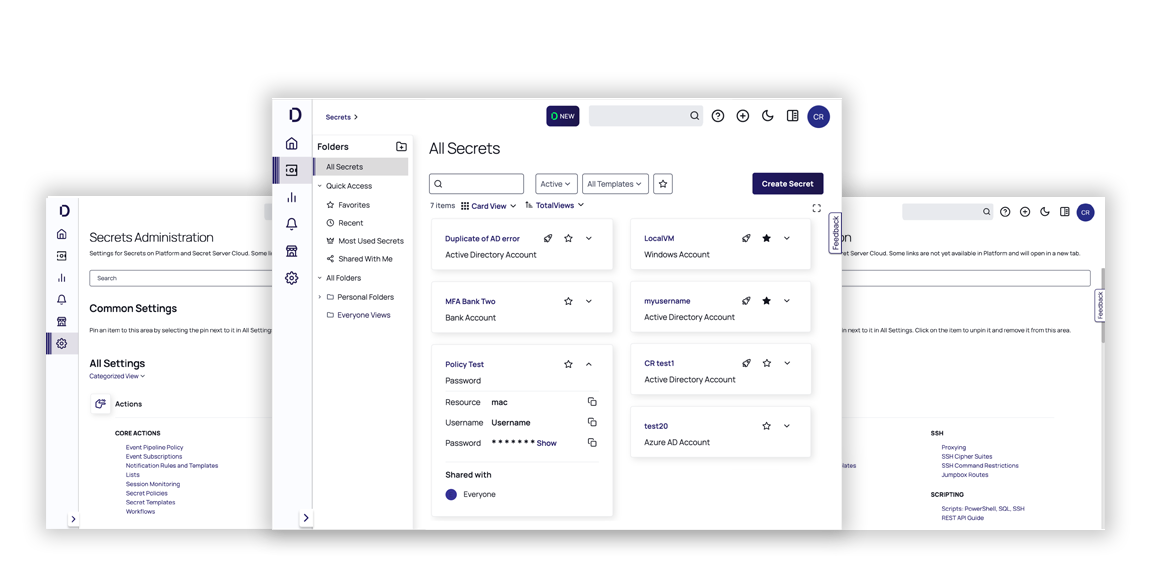
Secret Server
Protect your privileged accounts with our enterprise-grade Privileged Access Management (PAM) solution.
Available both on-premise or on the cloud-native Delinea Platform

Enterprise-scale Privileged Access Management at lightning speed
Get started quickly
Get up and running fast with solutions for privileged account discovery, turnkey installation and out-of-the-box auditing and reporting tools.
Scale for growth
Manage multiple databases, software applications, hypervisors, network devices, and security tools, even in large-scale, distributed environments.
Customize as you like
Create endless customizations with direct control to on-premise and cloud PAM. Work with professional services or use your own experts.
Establish secure vault
Store privileged credentials in an encrypted, centralized vault with the option to enable quantum-safe encryption
Discover privileges
Identify all service, application, administrator, and root accounts to curb sprawl and gain a full view of your privileged access.
Manage secrets
Provision and deprovision, ensure password complexity and rotate credentials.
Delegate access
Set up RBAC, workflow for access requests, and approvals for third parties.
Control sessions
Implement session launching, proxies, monitoring, and recording.
Check out our interactive demos to experience these capabilities yourself.
Start a Free 30-Day Trial
Secret Server supports extended PAM
The standard definition of PAM isn’t sufficient for the growing risk of cyberattacks. We believe PAM must address the exploding number of identities and today’s IT complexities.
Our products provide effective authorization controls for an identity-centric approach to security.
CLOUD
Fully featured Privileged Access Management in the cloud
Fully featured scalable Privileged Access Management vaultCloud-native platform lets you sign up and start right away
No hardware or infrastructure cost with PAM in the cloud
No provisioning, patching, or maintenance overhead
Scalable as your PAM needs grow
Integrations Marketplace for full visibility
Protect highly privileged account access with quantum-safe encryption.
Fully integrated with the Delinea Platform
ON-PREMISE
Industry-leading Privileged Access Management for
in-house deployments
Total control over your end-to-end security systems and infrastructureDeploy software within your on-premise data center or your own virtual private cloud instance
Meet legal and regulatory obligations that require all data and systems to reside on-premise
Protect highly privileged account access with quantum-safe encryption.

Securing Tomorrow, Today: The Benefits and Best Practices of Quantum-Safe Encryption with Secret Server
Secret Server is the first Privileged Access Management vault to deliver quantum-safe encryption to ensure organizations are secure today and tomorrow. Watch this webinar to learn how easy it is to add quantum-safe encryption to your highly sensitive secrets.
Privileged Access Management for Dummies