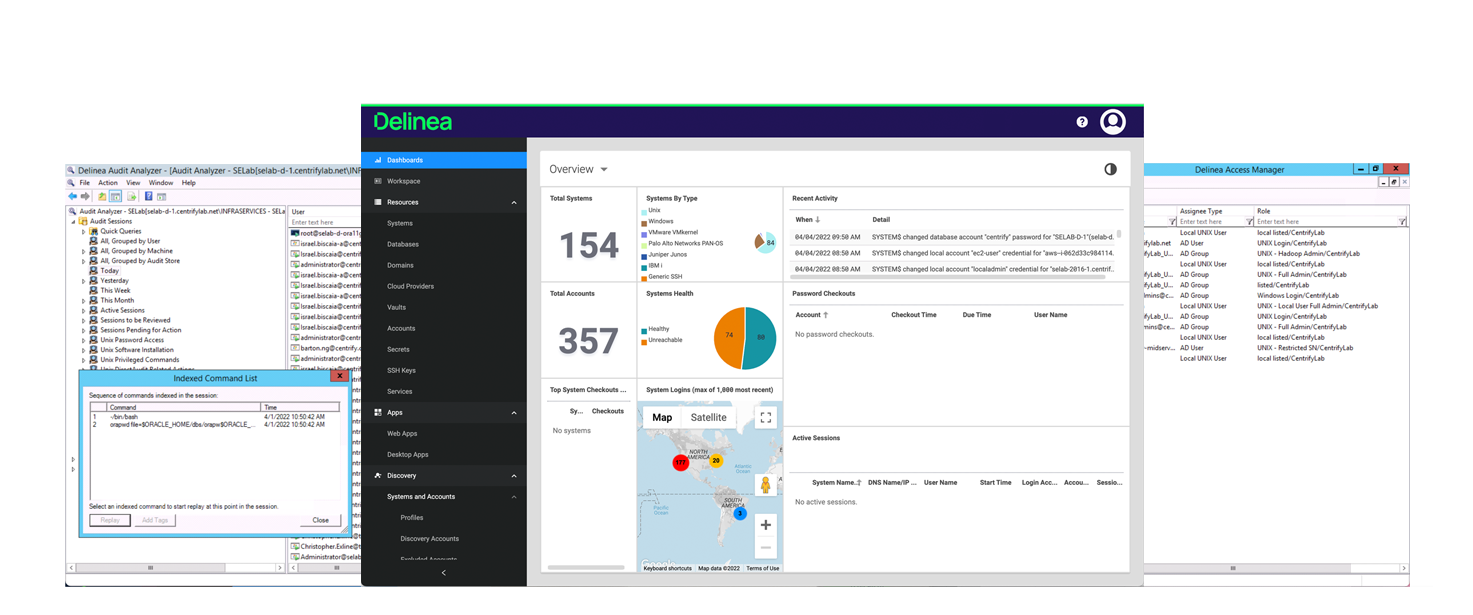
PART OF THE SERVER PAM SOLUTION
Server Suite
Enforce just-in-time and just-enough privileges for Linux, Unix, and Windows servers and centrally manage policies from Active Directory.
Delinea named a Leader again in the 2023 Gartner® Magic Quadrant™ for Privileged Access Management
Protect your servers against identity-based attacks
Simplify User
Authentication to Servers
Authentication to Servers
Easily consolidate complex and disparate identities for Linux and Unix natively within Microsoft Active Directory.
Reduce Administrative
Access Risks
Access Risks
Minimize the risk of a breach and reduce lateral movement with a flexible, just-in-time privilege elevation model.
Achieve Legal &
Regulatory Compliance
Regulatory Compliance
Advanced session recording, auditing, and compliance reporting aid forensic analysis into abuse of privilege.
Consolidate identities through Active Directory to centrally manage access, authentication, and privileges
Centralize discovery, management and user administration for Linux, Unix, and Windows systems to enable rapid identity consolidation natively into Active Directory using Delinea patented Zone technology. The results are higher levels of identity assurance and a significantly reduced attack surface with fewer identity silos, redundant identities, and local accounts.
Centrally manage identities
Manage privileged user and service accounts from Windows and Linux in Active Directory.
Support best practices
Align with regulations and best practices such as Zero Trust and zero standing privileges.
Enforce least privilege
Just-in-time, fine-grained access control with RBAC and our patented Zones technology.
Enforce adaptive MFA
Higher levels of identity assurance with Multi-Factor Authentication (MFA) at privilege elevation.
Improve compliance
Complete audit trail for security review, corrective action, and compliance reporting.
Modern, scalable architecture simplifies the management of complex AD infrastructures
Features |
|
Active Directory Bridging |
|
Machine Identity & Credential Management |
|
Local Account & Group Management |
|
Authentication Policy Management |
|
Group Policy Management |
|
MFA Enforcement at Login and Privilege Elevation |
|
Just-Enough Privilege |
|
Just-in-Time Privilege |
|
Consistent Security Policy Management |
|
Advanced Host-Based Session Recording, Auditing, and Reporting |
|
Part of Server PAM solution |
|
Download the Server PAM datasheet for more information.
Server Suite supports extended PAM
The standard definition of PAM isn’t sufficient for the growing risk of cyberattacks. We believe PAM must address the exploding number of identities and today’s IT complexities.
Our products provide effective authorization controls for an identity-centric approach to security.
Industry-leading PAM solution for AD-joined servers
Easily consolidate complex and disparate identities natively in Active Directory for greater security and manageability of privileged access to servers, while enforcing MFA for stronger identity assurance.
Enforce the principle of least privilege consistently across Linux, Unix, and Windows servers.
Identify abuse of privilege, thwart attacks, and easily prove regulatory compliance with a detailed audit trail and session recordings that capture all privileged activity on AD-joined servers.
Zero Trust Privilege for Dummies
Understand the basics of Zero Trust and its relevance to Privileged Access Management. Learn how to assess your organization’s Zero Trust maturity.
Delinea named a Leader in Forrester Wave Privileged Identity Management (PIM), Q4 2023
Learn why Delinea received the highest possible scores in the Vision, Roadmap, Resiliency and Performance, and Deployment Options criteria.
