PART OF THE SERVER PAM SOLUTION
Cloud Suite
Consolidate identities and leverage multiple directory services such as AD, OpenLDAP, Ping Identity,
and Azure AD, to enable modern enterprises to streamline privileged access to their servers.
Delinea named a Leader again in the 2022 Gartner® Magic Quadrant™ for Privileged Access Management
Reduce Identity
Management Complexity
Management Complexity
Simplify user authentication to servers leveraging multiple-directory services, including AD, OpenLDAP, and cloud directories such as Ping Identity and Azure AD.
Implement Privilege
Elevation Best Practices
Elevation Best Practices
Enforce the principle of least privilege with just-in-time and just enough privilege to minimize the risk of a security breach.
Expedite Security
Incident Investigations
Incident Investigations
Identify abuse of privilege, thwart attacks, and quickly prove regulatory compliance with a detailed audit trail and video recordings.
Centrally control Identities and leverage multiple-directory services to secure access and protect against identity-based cyberattacks.
Delinea’s cloud-based SaaS solution consolidates identities and applies Zero Trust Principles to stop privileged access abuse and reduce security risks. Cloud Suite allows organizations to minimize their attack surface by consolidating identities and leveraging multi-directory services for authentication, implementing just-in-time privilege, MFA enforcement, and securing remote access while auditing everything.
Why Delinea Cloud Suite?
Simplify user authentication
Single enterprise identity to securely log in to any server.
Minimize risk with Zero Standing Privileges
Flexible, just-in-time model with privilege elevation.
Manage access for non-human identities
Centrally manage security policies for users, machines, and applications.
Enforce adaptive MFA
Apply MFA policies consistently across all your regulated and business-critical systems.
Improve security and compliance
Watch privileged sessions in real-time and instantly terminate suspicious sessions
Unified PAM platform for managing privileged access in multi-cloud infrastructure
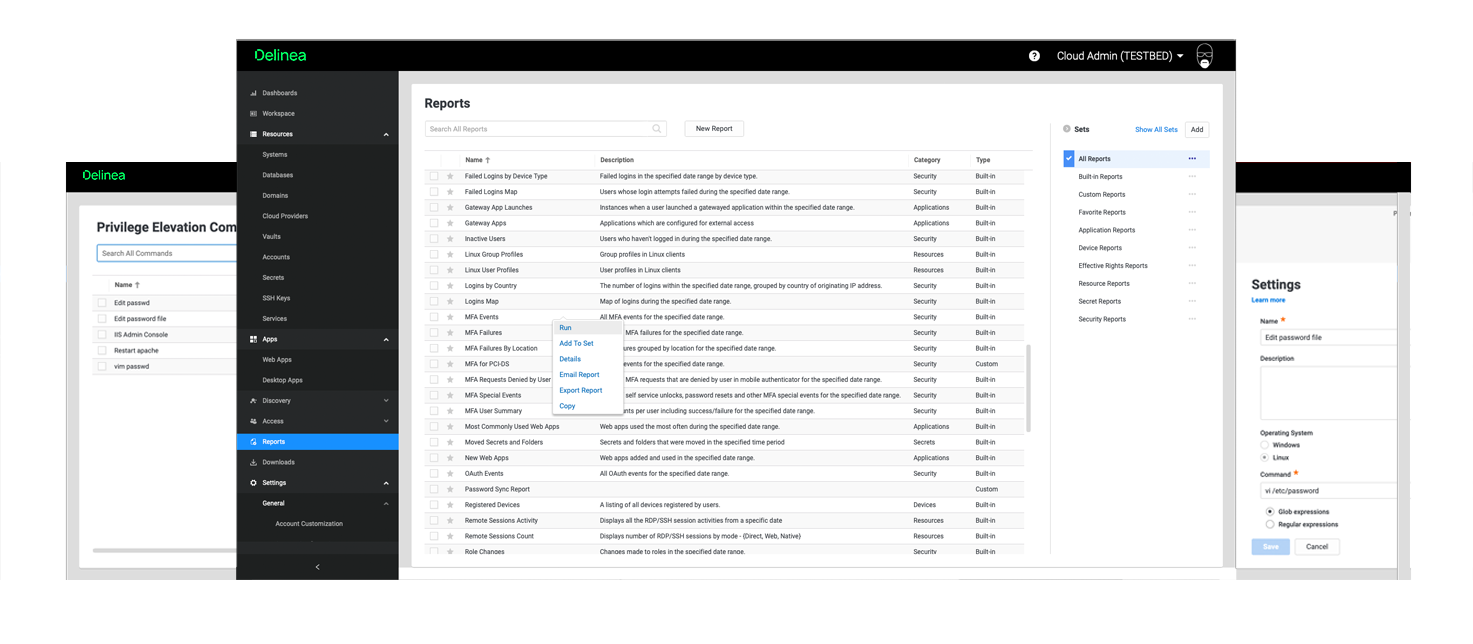
Features |
|
Hub and spoke architecture |
|
Cloud privilege elevation |
|
Unified policy management |
|
MFA enforcement at login and privilege elevation |
|
Allow trusted machine identities |
|
Multi-directory brokering |
|
Delegated machine credentials |
|
Advanced host-based session recording, auditing, and reporting |
|
Gateway session recording, monitoring & control |
|
Part of Server PAM solution |
|
Download the Server PAM datasheet for more information.
Cloud Suite supports extended PAM
The standard definition of PAM isn’t sufficient for the growing risk of cyberattacks. We believe PAM must address the exploding number of identities and today’s IT complexities.
Our products provide effective authorization controls for an identity-centric approach to security.
Industry-leading PAM solution for enabling identity consolidation and leveraging multi-directory services transformation at scale
Easily accommodates identity consolidation in demanding and complicated multi-cloud architectures
Minimal hardware or infrastructure costs with PAM in the cloud
Meet regulatory compliance and simplify the forensic investigation of cloud provider instances

Free eBook: Zero Trust Privilege for Dummies
Understand the basics of Zero Trust and its relevance to privileged access management. Learn how to assess your organization’s Zero Trust maturity.